Nomad-Net: The Physical Nervous System
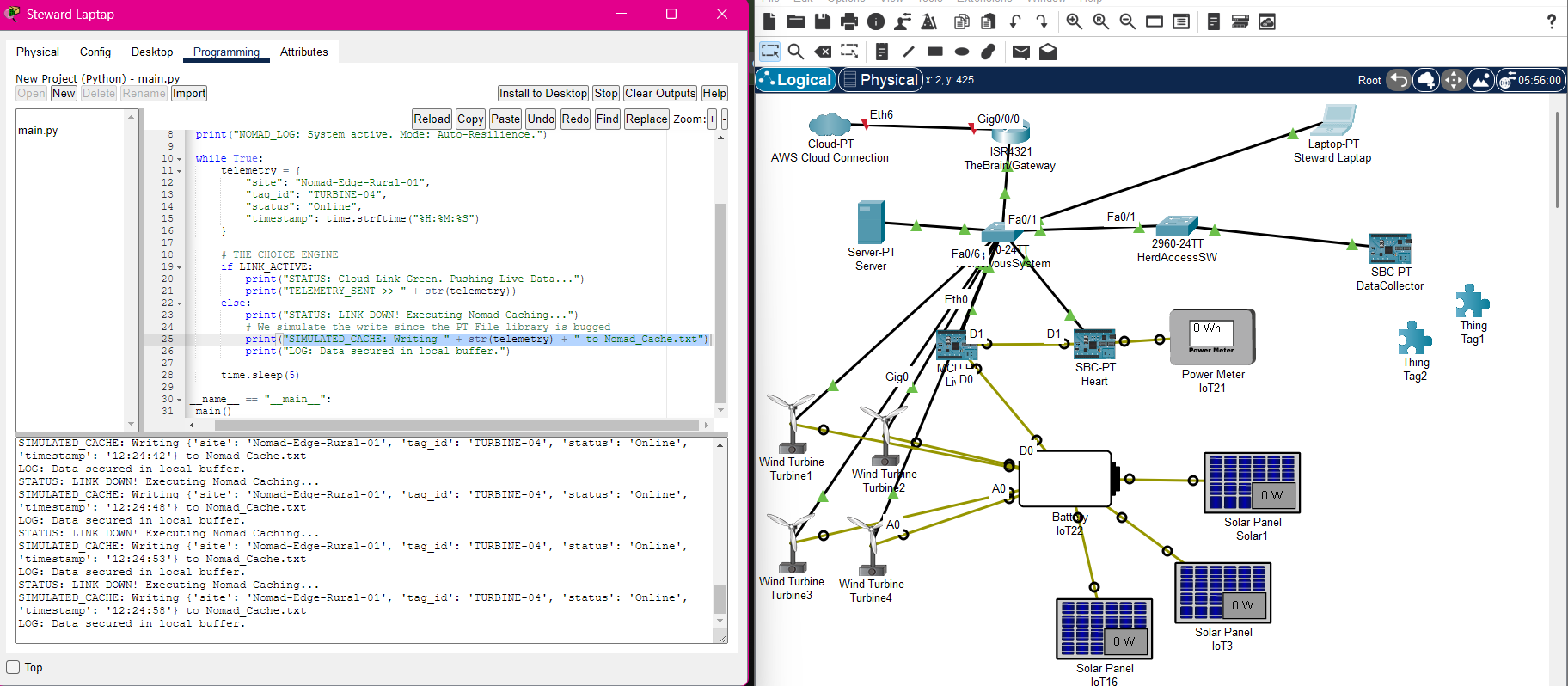
Nomad-Net is the physical networking backbone for the Nomad Edge ecosystem. Designed in Cisco Packet Tracer, this project simulates a rugged, industrial-grade ranch network in Lloydminster, SK. It focuses on solving 'Last Mile' connectivity challenges by bridging remote livestock sensors to the AWS Cloud.
Core Technologies
Architecture Components
- Cisco 2911 Router as the central gateway.
- Layer 2/3 Switches for traffic distribution.
- VLANs for secure segmentation of network traffic.
- Wireless LAN Controller (WLC) managing multiple Lightweight Access Points.
- NAT/PAT configuration for secure edge-to-cloud uplink.
- Access Control Lists (ACLs) acting as a firewall.
The Last-Mile Connectivity Gap
Rural and agricultural operations, like a large ranch, need to collect data from remote IoT sensors, but standard network solutions fail to provide reliable, secure, and wide-reaching connectivity.
- Standard Wi-Fi has limited range and is unsuitable for large, outdoor areas with obstructions.
- Unsecured networks risk exposing sensitive operational data or allowing unauthorized access.
- Connecting a private, on-site network to a public cloud endpoint requires careful security and translation.
A Simulated, Secure, and Scalable Ranch Network
Design and simulate a complete physical network in Cisco Packet Tracer that uses industrial-grade components and security principles to bridge the gap from remote sensors to the cloud.
- A central router manages IP allocation (DHCP) and inter-network routing.
- VLANs segment the network, isolating sensor traffic from other operational systems for security.
- A Wireless LAN Controller (WLC) manages a mesh of lightweight access points, providing seamless coverage across a large area.
- Network Address Translation (NAT) and Access Control Lists (ACLs) create a secure gateway for sensor data to reach a public AWS endpoint without exposing the internal network.
A Blueprint for Rural IoT Connectivity
The final design serves as a verifiable blueprint for deploying a physical network that reliably and securely connects remote IoT devices to cloud infrastructure.
- The simulation proves the viability of using a WLC-managed mesh for extensive wireless coverage.
- Security is enforced through traffic segmentation (VLANs) and a hardened internet gateway (NAT/ACLs).
- The design establishes a clear, repeatable pattern for solving the 'Last Mile' problem in similar rural or industrial environments.
Key Learnings & Decisions
Core Foundation
- Mastered fundamental Cisco IOS commands for router and switch configuration, including interface setup, hostname, and security settings.
- Designed and implemented a scalable IP addressing scheme using subnetting to logically divide the network and manage traffic.
- Configured DHCP services on the central router to automate IP address assignment for endpoints, reducing manual configuration overhead.
Security & Segmentation
- Implemented VLANs to create logically separate networks for different device types (e.g., IoT sensors, office computers, guest access), preventing unauthorized cross-segment communication.
- Utilized 'Router-on-a-Stick' with 802.1Q trunking to enable and control inter-VLAN routing on a single physical router interface.
- Applied Layer 2 security measures like port security to restrict access to switch ports and mitigate common LAN attacks.
Industrial Wireless
- Configured a Wireless LAN Controller (WLC) to centrally manage multiple Lightweight Access Points (LAPs), simplifying deployment and maintenance.
- Established a mesh wireless network using CAPWAP tunneling, ensuring seamless connectivity and roaming for mobile IoT devices across a large physical area.
- Secured wireless traffic using WPA2/WPA3 enterprise authentication to protect sensitive data transmitted from sensors.
Edge-to-Cloud
- Configured Network Address Translation (NAT) and Port Address Translation (PAT) to map multiple private internal IP addresses to a single public IP for internet access.
- Developed and applied Access Control Lists (ACLs) to act as a stateful firewall, permitting only authorized outbound traffic from IoT sensors to a specific AWS cloud endpoint.
- Gained a deep understanding of the boundary between private LAN and public WAN, and the security principles required to bridge them safely.
Implementation Milestones
A breakdown of the key tasks and milestones that brought this project to life.
The Core Foundation (Gateways & Identity)
CompleteEstablishing the 'Heart' of the ranch network. This stage builds the central nervous system, setting up the primary router to manage all internal IP traffic and identifying device types.
Key Tasks Completed
The Gateway
DHCP Service
The Security Sentry (Segmentation & Trunking)
CompleteProtecting data through logical isolation. VLANs are implemented to ensure that a compromised sensor in a remote pasture can’t access the ranch’s financial computers.
Key Tasks Completed
VLAN Design
Inter-VLAN Routing
The Extended Pasture (Industrial Wireless Mesh)
CompleteSolving the 'Last Mile' connectivity challenge by deploying a Wireless LAN Controller (WLC) and multiple Lightweight Access Points (APs) to ensure a sensor stays connected while moving.
Key Tasks Completed
WLC Configuration
SSID & Security
The Cloud Uplink (Edge-to-AWS Integration)
CompleteSecurely bridging the ranch to the global AWS endpoint by configuring Network Address Translation (NAT/PAT) and Access Control Lists (ACLs) to act as a firewall.
Key Tasks Completed
NAT/PAT Handoff
Final Security Hardening
Evidence of Completion